Securing a computer goes beyond more than just using strong passwords. You should consider what happens if an unauthorized person gains physical access to your computer. If the only security feature protecting your data from an unauthorized person is a user account password, then you have not taken enough steps to protect your computer and your data. This article presents all the steps you should take to enhance the physical security profile of your desktop/laptop computer running a Linux distribution.

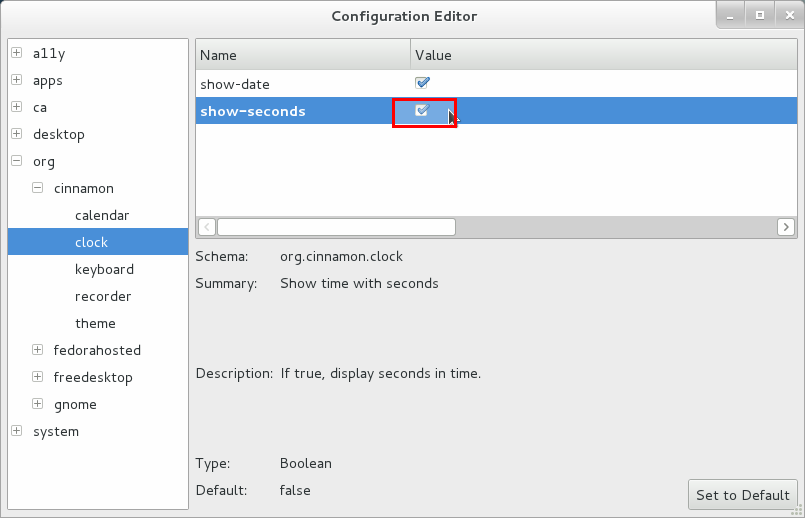
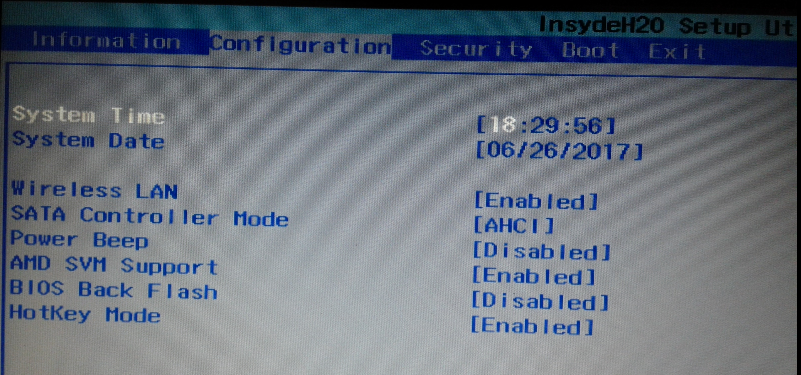
- Set a UEFI/BIOS Password – By default PC vendors generally configure their computers to boot from the hard disk and, failing that, to boot from removable media. You can change this boot order from the UEFI/BIOS setup utility. Which means anybody with physical access to the computer can do it too, not just you. To prevent unauthorized persons from accessing the UEFI/BIOS setup utility, you should enable the UEFI/BIOS password. Enabling the UEFI/BIOS password may also be used to prevent the system from booting.
Let me illustrate with this scenario. Let’s say some bad guy gains physical access to your computer and that computer was configured to boot from the hard disk and the UEFI/BIOS password was not enabled. To dispense with the headache of having to guess your username and/or password, Mr. Bad Guy could access the UEFI/BIOS and change the boot order so that the computer boots from removable media. Now he can pop in a live distro, boot the computer, mount the drive and … imagine how the story ends.
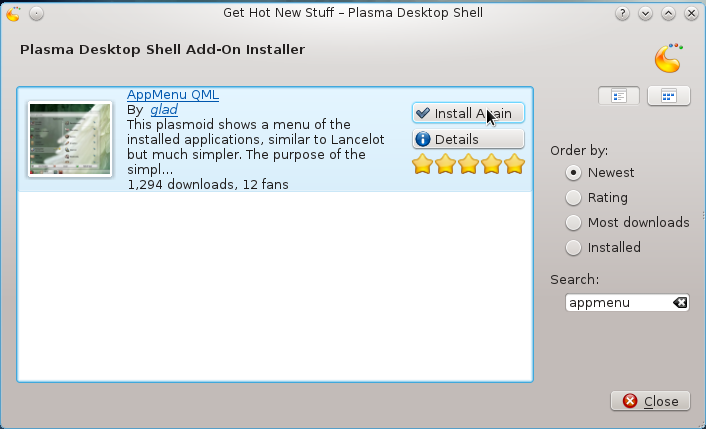
- Password-protect the boot loader – Password-protecting GRUB (GRand Unified Bootloader) 2, the boot loader/boot manager you will most likely be using on a Linux distribution is not commonly done, but it’s possible. Setting a bootloader password ensures that no one with unauthorized physical access to your computer will be able to gain access to single user mode. It also locks access to GRUB’s console. The command to accomplish that on a running system is grub-mkpasswd-pbkdf2. See this link for an example of how to password-protect GRUB on a running system.
- Encrypt the hard drive – See this article for why you should encrypt your computer’s disk. It mainly gives an example of how Fedora, a Linux distribution, implements disk encryption in its installer. If you’ve not heard the news yet, Red Hat, the company that supports the development of Fedora, was recently acquired by IBM.
- Never use auto-login – When setting a user account password, most Linux distributions will warn you when the password is weak (especially for root). Concerning passwords, try as much as possible to adhere to the following:
- Always choose strong passwords, minimum of eight characters.
- Do not base the password on the username. If you are using a distribution that uses the traditional root account system, do not set the root password to be the same as the regular account password.
- Never enable the automatic login feature. Many Linux distributions have this feature. Do not use it. If you are just introducing your kid or spouse to Linux, do not enable this feature for them. It is a bad security practice. Teach them the value of setting a password from the beginning.
- Implement Password Aging – Setting a password for expire, password-aging, is rarely enabled on the desktop, but it’s a feature that’s available in Linux. The graphical user management program on most Linux distributions will allow you to set your passwords to expire at a certain date. An expiration time of six months is the recommended.
If you implement all of the aforementioned tips on your Linux computers, give yourself a five star rating of paranoid. You are ultra secure (four star rating) if you implement steps 2 to 5, and secure (three star rating) if you implement only steps 3 to 5. Consider your security posture weak (two star rating) if you only implement steps 4 and 5 (user account password and password aging). You have a one star rating if you do not implement password aging. Smack yourself if you enable the automatic login feature.