BackBox is a Linux distribution that’s based on Ubuntu and designed for conducting “penetration tests and security assessments”.
If you’re not familiar with the distribution, this brief review will give you an idea what else it can be used for other than being an OS for pentesters.
My introduction to BackBox was with BackBox 3, and that was back in October 2012, when I published BackBox Linux 3 review.
Today’s review is of BackBox 4.3, the latest edition, which is based on Ubuntu 14.04 and ships with its own suite of security-focused applications. This puts it in the same niche as CAINE, Deft and Kali.
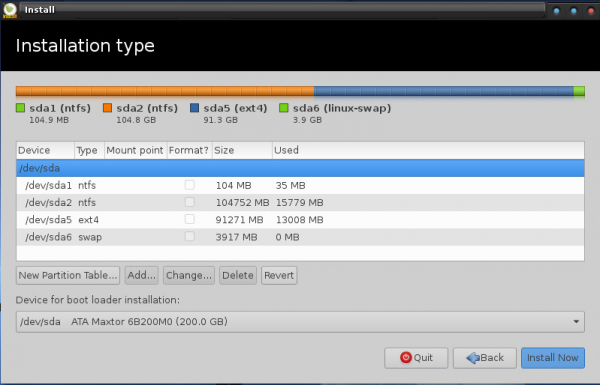
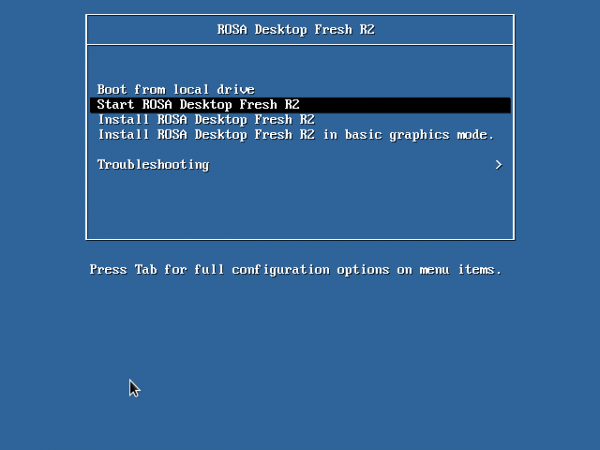
Installation Program: The graphical installer on BackBox 4.3 is the same as the one on its parent distribution. As such, it has support for full disk encryption and home folder encryption, two features which I think should be standard on the installer of any modern operating system. It also has support for LVM, the Linux Logical Volume Manager. LVM makes it easy to manage disk and disk partitions in Linux.
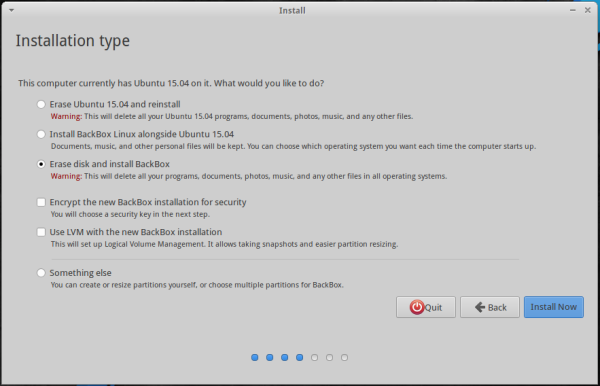
Figure 1: BackBox 4.3 graphical installer
Desktop: BackBox’s default desktop is the Xfce desktop environment, though the installed version (Xfce 4.11), is one revision behind the latest, stable version, which is Xfce 4.12.

Figure 2: Default desktop of BackBox 4.3.
Figure 3 shows the default desktop with the menu in view.
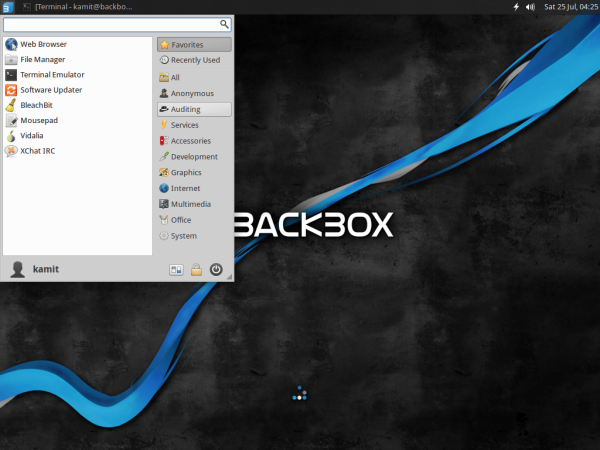
Figure 3: Default desktop of BackBox 4.3 showing the Xfce menu.
Applications: Though BackBox is designed for security professionals, it comes with a full suite of normal desktop applications. So you’ll find pre-installed a complete Office suite in LibreOffice, as well as standard Internet, multimedia and graphics applications. So even if you’re not a security professional, you can still use BackBox 4.3 like any other desktop distribution.
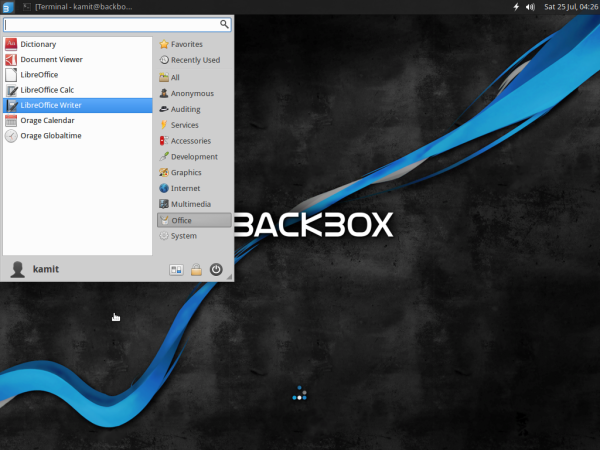
Figure 4: LibreOffice is the default Office suite on BackBox 4.3.
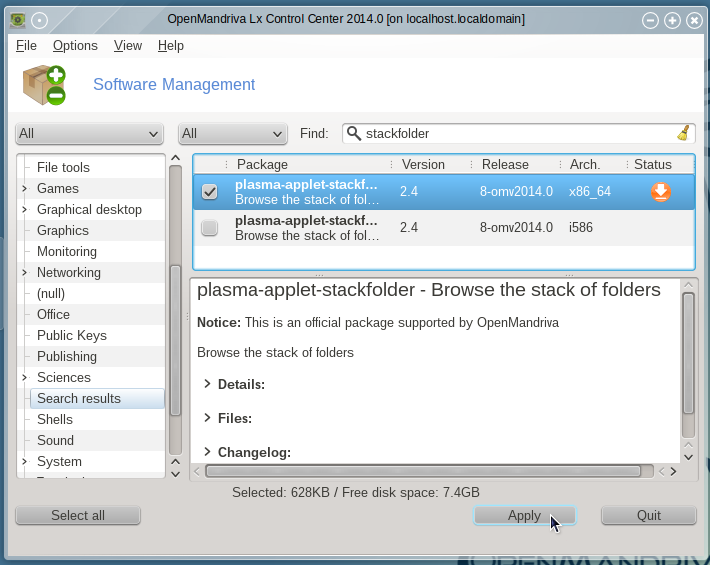
For managing applications, Synaptic Package Manager is the installed graphical package manager. If you prefer a more modern graphical application manager, Ubuntu Software Center is in the repository.
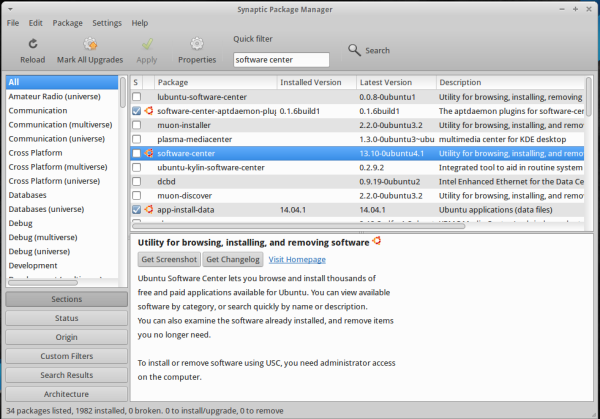
Figure 5: Synaptic Package Manager on BackBox 4.3
For security professionals and non-security professionals who would like to use specialized security applications for conducting “penetration tests and security assessments”, BackBox 4.3 comes with the best open source/free software applications for performing such tasks. You’ll find them all under the Auditing menu category. Available options include applications for wireless scanning and cracking, VoIP analysis, mobile analysis of Android and iPhone smart devices, information gathering, social engineering, reverse engineering, etc.
And you don’t even have to be an expert to use most of the applications. A basic understanding of the subject matter is all you need, plus the ability to read simple man pages and some familiarity with the Linux command line.
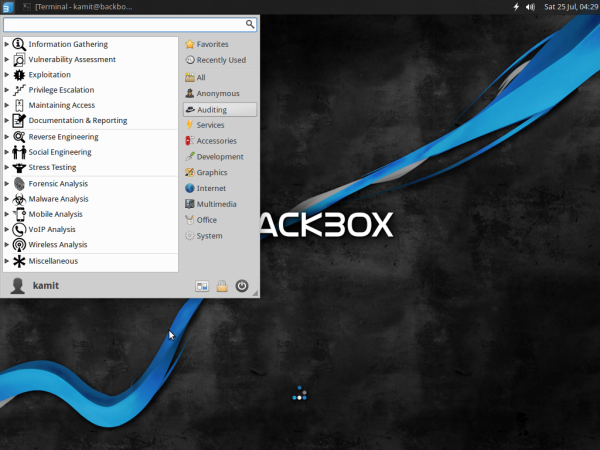
Figure 6: Category of security auditing applications on BackBox 4.3.
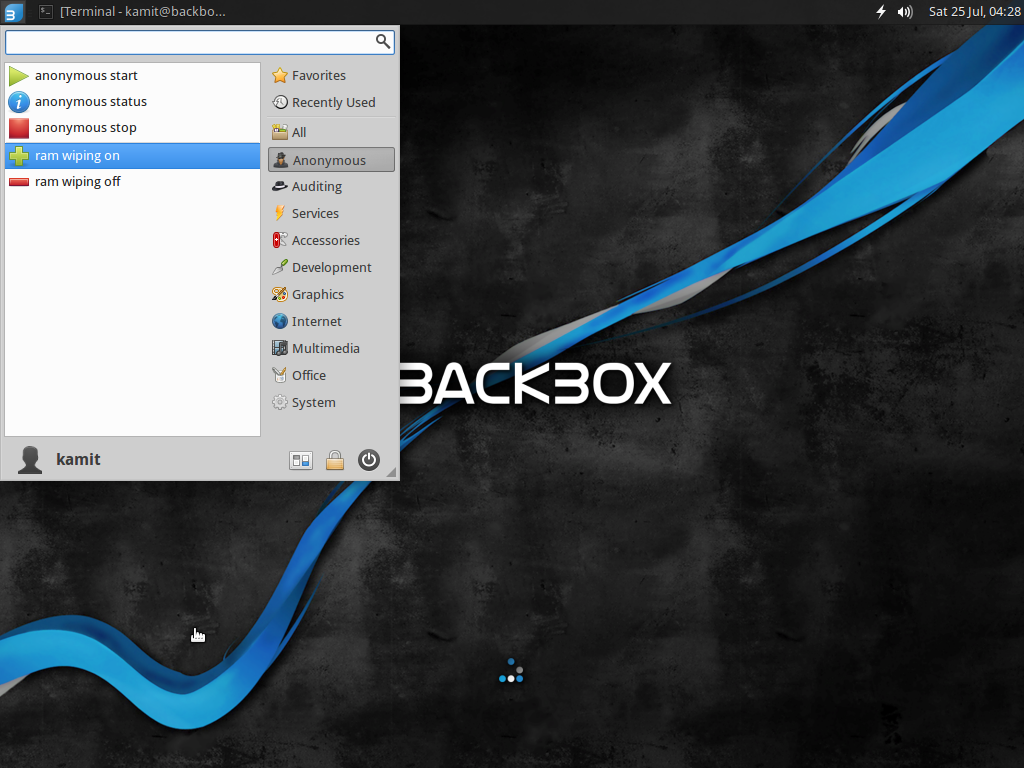
Aside from standard desktop and security auditing applications, Tor, the anonymizing application, and it’s helper applications are fully integrated into BackBox so that all you need to surf the Web like a secret agent is start the Tor service by clicking Services > Tor > tor start.
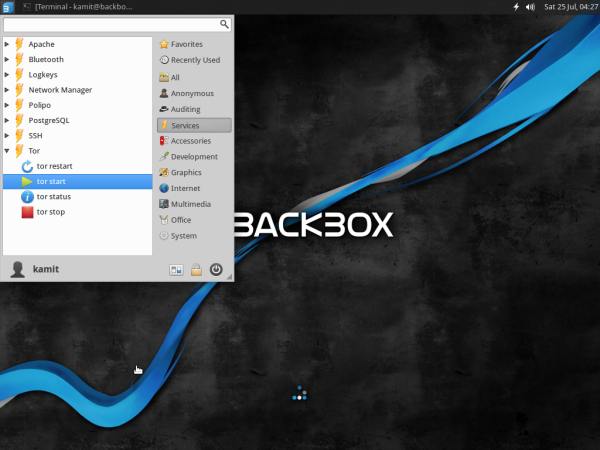
Figure 7: How to start the Tor service on BackBox 4.3
Then Anonymous > anonymous start and follow the command line prompts. Aside from making it easy to cloak your true digital footprint, BackBox 4.3 also includes a feature that you can turn on so that it wipes your RAM on shutdown. As shown in this image, access to that feature is via Anonymous > ram wiping on.
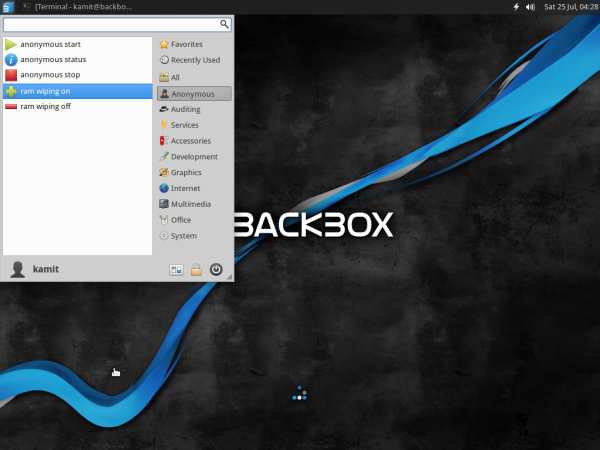
Figure 8: How to start the Tor service on BackBox 4.3
Internal Security: Unlike Linux Mint, which has most of the internal security tools and applications it inherited from Ubuntu stripped, BackBox 4.3 has all those features in place. AppArmor, for example, is active:
$ sudo apparmor_status apparmor module is loaded. 17 profiles are loaded. 17 profiles are in enforce mode. /usr/bin/evince-thumbnailer//sanitized_helper /usr/bin/evince//sanitized_helper /usr/bin/vidalia ... /usr/sbin/cupsd /usr/sbin/tcpdump system_tor 0 profiles are in complain mode. 2 processes have profiles defined. 2 processes are in enforce mode. /usr/sbin/cups-browsed (999) /usr/sbin/cupsd (1492) 0 processes are in complain mode. 0 processes are unconfined but have a profile defined.
Aside from AppArmor, which is an application-level firewall, UFW, the network firewall, is also installed, but inactive. Enabling UFW should top the list of task you complete after installing BackBox 4.3. A better alternative, which is also in the repository, is FirewallD, a firewall application with support for network zones.
To sum: So BackBox 4.3 is great for conducting penetration tests and security assessments, which is cool. The coolest, I think, is the default installation has been made very friendly for non-experts and can be used just like any other desktop Linux distribution. So if you wish to play with a Linux distribution designed for the hacker-type, BackBox 4.3 is a good choice.
Resources: You may read the Release Notes of BackBox 4.3 here and download an installation image for your platform here. Installation images for 32- and 64-bit platforms are available.