Released just a few days ago, GNOME 3 is the latest major version of the GNOME desktop environment. If you are currently running a GNOME-based Linux or BSD distribution, you are probably using version 2.30 or 2.32, but that should change in the upcoming release cycle when many of the distributions will be shipping with GNOME 3 as the default. So while we wait, this article will attempt to give you an idea of what to expect. Rather than discuss the difference between old and new GNOME from the development angle, the article presents information from a lay user’s perspective. Can I find my away around the new desktop without consulting a manual or documentation?
If you are interested in how GNOME 3 came to be, try this link, and this.
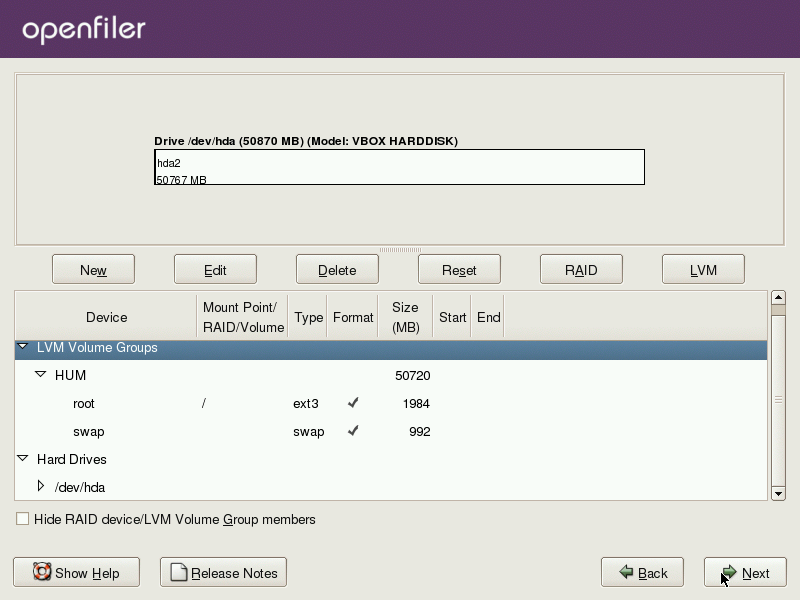
GNOME will not run on just any computer, so if your computer does not meet the hardware and driver requirements, you will see the message below. Now we know that GNOME can run in two modes – the Standard GNOME 3 mode, and in Fallback Mode. In Fallback Mode, you get a desktop experience very close to the GNOME 2 desktop. In a sense, it is an hybrid mode, not quite GNOME 2 and certainly not Standard GNOME 3.

Here’s is what the GNOME desktop looks like in Fallback Mode. The Top and bottom panels are still in place, and the Applications and Places menu still occupy their usual place on the top panel. You can see that the administrative tools which used to be under System > Administration, right next to the Places menu, are now accessible from Applications > System Tools. What about all the administrative tools that used to be under System > Preferences?

Well, those are now accessible from System User > System Settings. More on System Settings tools further down.

If your computer can run GNOME 3 in all its glory, your desktop will look just like the image below shows. Notice that the Applications and Places menu have been replaced by the Activities menu. The “Displays” entry right next to it is for an open application, and not a permanent entry on the top panel. Did you notice that there is no bottom panel? Did you also notice how snazzy and cool the menus look.

Clicking on Activities reveals real side of the desktop. All open windows are visible on the main part of the desktop. To the left is the favorites and open applications dock. The right “panel”, which is retracted by default, and visible on mouseover, is like the virtual workspace switcher.

Clicking on Applications takes you to what you might call the menu. From here, you can use the search box to locate applications or just look in the applications categories. You add applications to the Dock by right-clicking on an application’s icon and selecting “Add to Favorites.”

This is just to show how to add an application to the Dock.

You can see the accessibility features enabled by clicking on the Assistive Technologies icon on the top panel. This is not available on the top panel in Fallback Mode.

While in the Windows view, you can open the controls of Rhythmbox or any other application applet in the Messaging Tray.






Hi, thanks for the review!
I’m wondering if I can install it on my pc, on old AMD Athlon, 1,2 Ghz with only 262 RAM..
It has a WinTVExpress PAL/SECAM tuner (44806), and that’s almost the only thing I really need to have working… Do you think I can have drivers and WinTV working if I install Gnome 3?
Many thanks!
I am Windows 7 user who is willing to switch to a Linux distro. I tried Ubuntu 10 and Linux Mint 11 and like them. Now, as I finally decided to make the full switch, all the main distros are using crap shells. And of course, I don’t want to install a distro with which I will be stuck in the future. So now the decision is very hard for me. Looking for an alternative to the Unity and Gnome 3 garbage. Unity isn’t that bad, I have to say. But after trying the live cd for 2 weeks, too many things got into my way for the simplest tasks. So I tried a Gnome 3 desktop, but it’s even worse — just on another level. Gnome 3 is the stupidest thing I ever tried so far. Ubuntu and Mint went down the hill with their decision to implement these garbage shells. I am currently trying openSUSE with KDE desktop. This seems the only alternative that’s left. Too bad that exactly Linux developers do everything wrong that MS did wrong in the past.
Yep, KDE is the way to go.
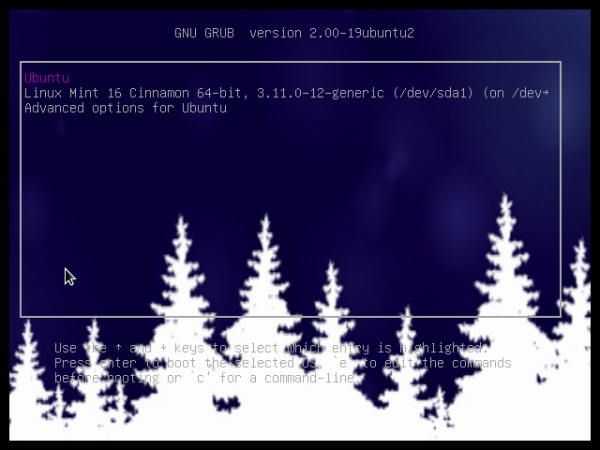
I install openSUSE 12.1 in Virtualbox and i still can’t make the GNOME 3 GUI work. Still fallback mode. 🙁
I recently switched to ubuntu 11.04 and wanted to give unity a try, it felt unresponsive at first but I got the hang of it in 2 to 3 days and started to work my way well through all the complications, I have been reading about gnome 3 shell and how its better than unity so I decided to install it to replace unity and after it it was done I immediately noticed my desktop felt lonely, it felt like I was staring into a wallpaper and not my desktop, im just not one of those people who like a clean desktop, i missed the unity bar immediately, the no minimize button is also confusing in gnome, to me unity maintains some of the old features while bringing in a lot of new ones at the same time and it seems to me like a nice change, im sure unity will develop over time and it will surely stand out
gnome 3 is way better than unity. ubuntu will fail for not giving users what they want
Gnome (s)hell is a horrible mess. It’s slow, unusable and just plain ugly.
I just hate the new GNOME 3, they totally messed it up, almost as bad as Unity. All this has for the first time made me look at alternatives and so far I’m positively surprised with KDE. I’m starting to like kDE so much that I’m currently trying out various KDE distributions so I can see which one is the best for replacing Ubuntu later.
Support for older, less powerful computers is a concern that I have with Gnome 3. First of all I read that they will be working to make the graphic requirements lower for the main version. I have not read, but I believe, that they will put some more time into the fallback version, and make it work more like the main version.
GNOME 3 is super-fast and stable. I have the (subjective) feeling that the virtual desktops and the lack of visible application notifiers make it easier to concentrate on the task at hand; you work on one desktop and just forget about the others. Until an incoming mail or something else asks for your attention by sliding in from the bottom of the screen.
It looks awful and Gnome Shell makes things harder than they used to be. An only thing which looks better is desktop. Applications remained the same. Same ugly icons, ugly theme. Sadly, Gnome Shell is slow and unstable. However, what’s the most irritating is lack of basic features which are important on every usable desktop. There’s no way to change fonts till someone installs third party hack tool. Launching and managing applications became harder too.
Hi, I have been using Gnome3 on Opensuse from last 3 days and it simply rocks (better than unity). It does add subtle usability to your daily tasks which one doesn’t realize immediately.Its certainly better than Gnome2 and I hope any minor kinks will be ironed out soon.