Recently, Mathy Vanhoef of imec-DistriNet, KU Leuven, discovered a serious weakness in WPA2 known as the Key Reinstallation AttaCK (or KRACK) attack. Their overview, Key Reinstallation Attacks: Breaking WPA2 by forcing nonce reuse, and research paper (Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2, co-authored by Frank Piessens) have created quite a stir in our industry because the press touts that it “breaks Wi-Fi”.
There have been numerous articles written about this vulnerability, and we won’t rehash them here. However, we want to take a moment to talk about how this relates to Kali Linux, from a defensive, testing, and detection standpoint.
Is Kali Linux Vulnerable?
From a defensive standpoint, if you’re keeping up with your Kali Linux rolling updates (via a simple “apt update && apt upgrade), you’re already patched against this vulnerability thanks to patches in wpasupplicant and hostapd (both at 2.4-1.1). To be entirely clear: an updated version of Kali Linux is not vulnerable to this attack. You are keeping your Kali Linux system up-to-date, aren’t you?
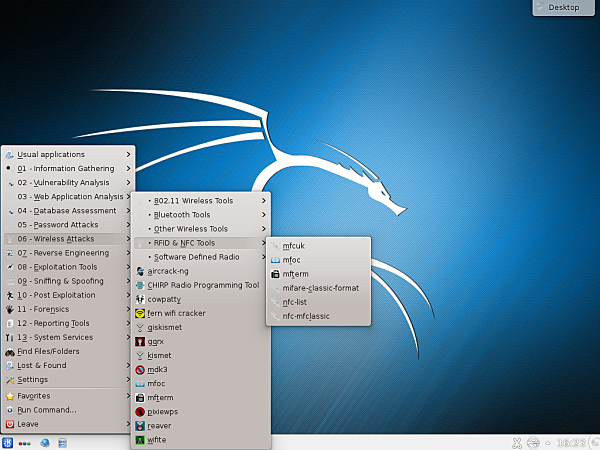
How do I test for the Vulnerability?
Find out by clicking here.