Editor: Kali Linux is a special Linux distribution designed just for penetration testing, or pentesting. It is based on Debian Testing, and is one of a handful of such distributions in active development.
In this blog, I describe how you can deploy Kali Linux and run penetration testing (also called pen testing) on AWS or Google Cloud using Ravello System’s nested virtualization technology.
This ‘Linux/Web Security Lab’ lets you hit the ground running in a matter of minutes and start exploiting security vulnerabilities. By the way, if you haven’t already seen it, this blog by SimSpace about on-demand Cyber Ranges on Ravello is very interesting as well.
You’ve been living under a rock if you haven’t noticed the high profile security breaches that have shaken the technology industry in recent years. From huge government spying scandals to the countless company databases infiltrations, we have never been more aware of the need for securing the complex systems on which we so heavily rely on.
Security awareness is at an all-time high, but the information security profession largely still remains out of reach for most in the tech industry. What exactly do penetration testers do? How does fuzzing or reverse engineering help to make networks and systems more secure? This blog post aims to help give beginners and security amateurs some hands-on experience in using popular systems and tools used by security professionals to help keep those black hats out.
Read the complete article here.
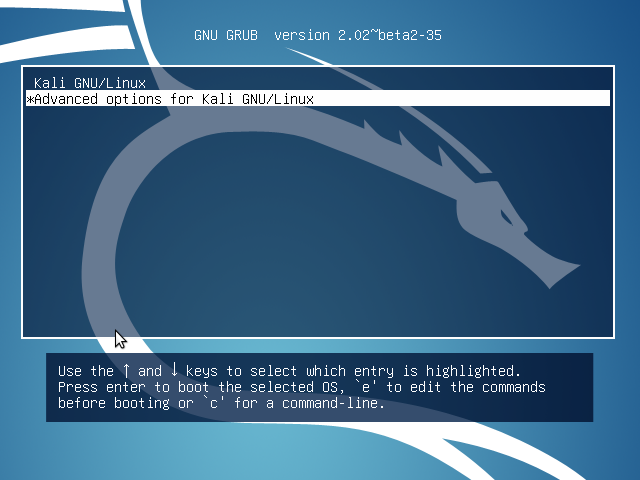
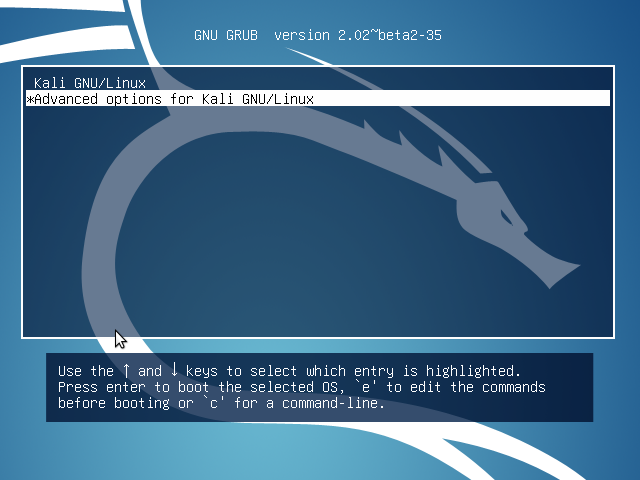
GRUB menu of a Kali Rolling installation
When you’ve finished building your pentest lab using Kali Linux, Metasploitable and WebGoat, take another step and enhance your ethical hacking and online penetration testing skills by requesting a free video course of Online Penetration Testing and Ethical Hacking.