Today’s vulnerabilities – Heartbleed, Shellshock, Poodle – have a brand.
When vulnerabilities have a brand and your favorite companies are making front page news for getting hacked, you know enterprise security is due for a change. Although our everyday lives have been changed by the connection we have to the Internet though the Internet of Things, online apps and more, many enterprises’ server security practices have yet to change.
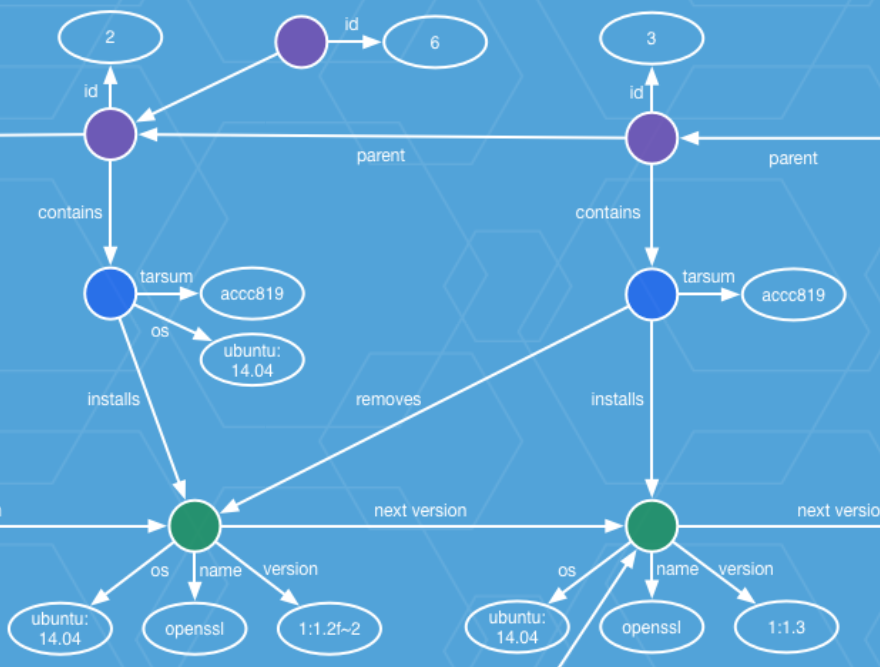
Today in our effort to continue our CoreOS mission to secure the Internet, we are making it possible to better protect against everyday threats. We started this mission with CoreOS Linux, where we provide automatic security and software patches to all servers. We led the industry forward with container security pioneered by rkt, and then again with Clair, the open source container vulnerability assessment tool.
And today we take our mission one step further with the introduction of Distributed Trusted Computing for Tectonic Enterprise.
What is Distributed Trusted Computing? Continue reading.

Distributed Trusted Computing for Tectonic Enterprise