Thanks to a very strict password policy and one too many passwords to remember, I managed to forget both the root and user account passwords of a test Fedora 21 installation. I could have reinstalled the whole system, but decided that the situation presented a good opportunity to attempt a password recovery.
Luckily, performing a password reset operation on a Linux distribution is a relatively simple operation. So simple that anybody with physical access to your computer can do it. That means anybody, whether they are authorized to or not.
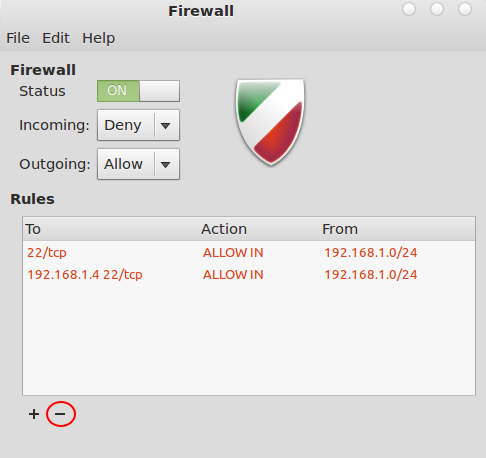
And that presents a good case why users should always configure full disk encryption and/or password-protect GRUB, the default bootloader on virtually all Linux distributions.
So what follows is a step-by-step guide on how to recover a password on Fedora 21. The same steps should apply to Fedora 20 and the upcoming Fedora 22. The password being reset can be the root password or a standard user account password.
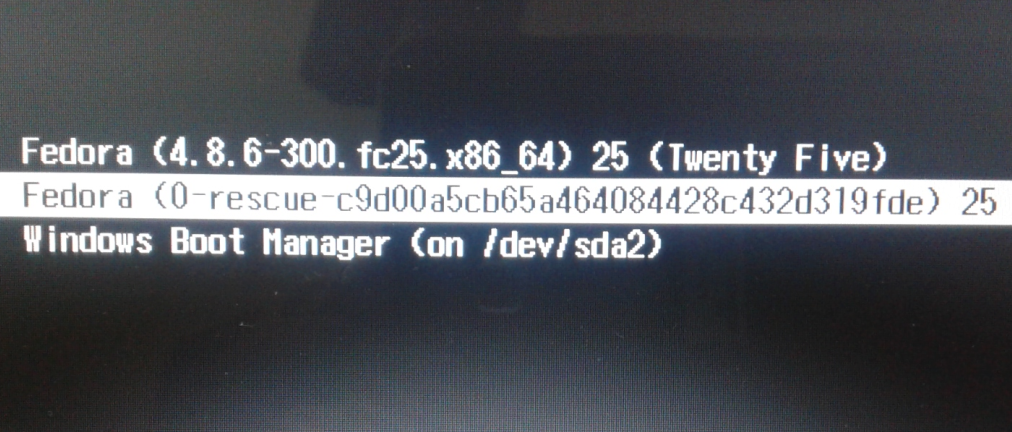
A password recovery attempt in Linux begins at the GRUB boot menu. Figure 1 shows what it looks like on Fedora 21, where the default entry is selected. That’s the entry that you’ll have to edit to begin the password reset operation. And that entails pressing the E key on the keyboard.
Afterwards, you’ll see a window like the one shown in Figure 2. There’s only one long line that you’ll need to edit, but you’ll have to scroll down to see it. To scroll down, keep pressing the Down arrow key on the keyboard until you get to a line that begins with linux16.
Figure 3 shows the options on that line. It’s a very long line, so you’ll have to use to Left arrow key to move the cursor until it reaches the end of the line. Note that the options span two lines. The line break is marked by the backslash (\).
To reset the password, the system has to be booted into single user mode. To cause that to happen, add rw followed by a space then followed by init=/bin/bash to the end of the line. In the example shown in Figure 4, I had to type the new options on a new line. That’s the reason for the new backslash just before rw. After typing the new options, reboot by pressing Ctrl X.
The system will reboot into single user mode. In that mode, you’ll be operating with the privileges of the superuser. To emphasize, this is the reason why you should always password-protect GRUB or configure full disk encryption. Otherwise, any person that gains physical access to your computer can use this same method to reset the password.
To reset the password for the root account, type passwd, then press the ENTER key. To reset the password for a standard user account, type passwd followed by the target username. In the example shown in Figure 5, I reset the password of a user called kamit. In either case, you’ll be prompted to type the password twice. If the password-reset attempt is successful, the system will output passwd: all authentication tokens updated successfully.
Afterwards, type touch / .autorelabelto address an issue with SELinux. Finally, reboot the system by typing /sbin/reboot -f.
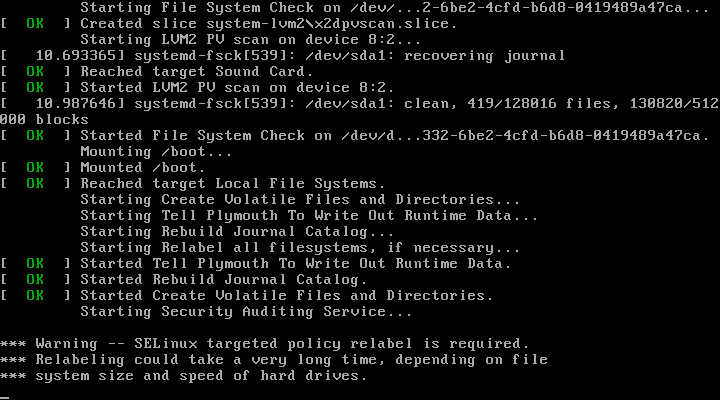
As the system reboots, there will be a brief pause at the juncture shown in Figure 7. Don’t worry, SELiux targeted policy relabeling takes just a couple of minutes. When rebooting has completed, you should be looking at a familiar login screen. Log in with the new password, if you changed the standard user password.












Thanks a lot…..This is worked for me.