So the third alpha release of what will become Fedora 22 has been released and I’ve managed to download ISO installation images of the main edition, which uses the GNOME 3 desktop, KDE and the Netinstall.
From those installation images, I’ve installed Fedora 22 alpha (GNOME 3), Fedora 22 KDE alpha, and Fedora 22 Cinnamon in virtual environments on my test desktop computer, which just happens to be running Fedora 21 KDE.
So far, I have nothing out of the ordinary to report with respect to the desktops themselves, but I do have a comment about Anaconda, the Fedora system installer.
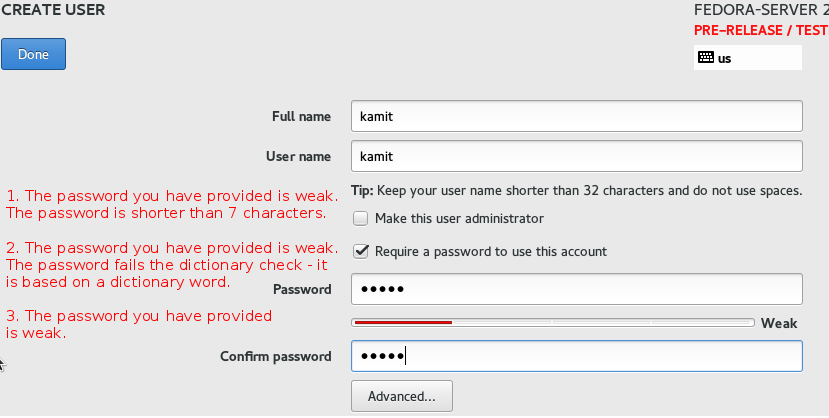
No, it’s not about all the UX design snafus that Anaconda is known for, but something different. And that something different is password strength enforcement. If you have installed one of the latest alpha releases, I’m sure you know what I’m talking about. If not, here’s what happens when you’re creating a user account and specifying a password for the root account.
Anaconda will not accept a password that’s less than seven characters. And no, a password that’s the same as the username, even if it’s more than seven characters, will not fly. If it contains the username in some form, that won’t fly too. In fact, if it’s deemed weak, Anaconda will not let you go past that step.
And that’s the problem: The definition of weak is too strict. So strict that even a password I use for online banking failed the test. And that’s an alphanumeric password with upper and lowercase letters. I can understand a very strict password enforcement for an online account, but for a desktop, yes, let’s be strict, but leave room for when you don’t really need to be paranoid.
Anybody from Fedora listening?
The image below shows the user setup step during the installation and some of the password strength test fail messages.







https://bugzilla.redhat.com/show_bug.cgi?id=1191842
Solved! 🙂
Good.
Just hoping Fedora team(s) will read this article.
=)
Just click on the button twice and anaconda will oblige, weakness of the password not withstanding. 🙂
No, that ws true on Fedora 21, not on 22.