Linux Mint Debian is a line of desktop distribution based on Debian, developed by the same group responsible for Linux Mint, a desktop distribution based on Ubuntu Desktop.
The latest edition, released on April 24, is Linux Mint Debian 201204. Made available for download were the Xfce and MATE/Cinnamon editions. Both editions have already being reviewed here and here.
While both editions just work out of the box, they leave a very important feature disabled by default. That feature, is the firewall. The really bad thing about this distribution is not just that the firewall is not configured, but that there are open ports that leave your computer wide open for Black Hats to mess with. So, if you are running a new installation of any of the editions of this current release of Linux Mint Debian, the first and most important thing to do, is enable and configure the firewall. This tutorial shows you how to do it. And it actually involves just a few mouse clicks.
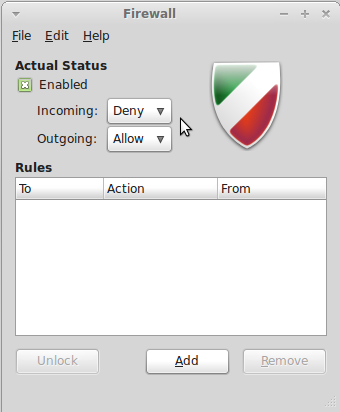
As on many Linux distributions, the firewall configuration utility is ufw, the Uncomplicated FireWall. It has three graphical interfaces that could be used to configure it. The only one available in the Linux Mint Debian repository is Gufw. While it is not as good as the others, it still gives you a user-friendly interface to get the job done.
Since it is installed by default, the only thing to do, is enable it. Launch it from the menu. You will find it under System > Firewall Configuration. It is shown below in its default state. To enable it, click the Unlock button.

After successful authentication, click the On/Off switch to enable it. The interface should now show some color. It is now enabled.

If you have no intention of allowing other computers to connect to any local service(s), you do not have to take any other action. No additional rule(s) is/are needed. The default rules, which allow all outgoing connections, while denying incoming connections that do not have a related entry in the State Table, is all the protection you need. If you need to add rules, this guide shows how to go about it.





-_-
You’re a real security freak..
empty words.
Why do so many people assume that there is only one computer on the local net? Since the firewalls used are non-standard (at least according to the UNIX command set), it takes some digging to figure out exactly how someone hosed local connectivity.
The better way to protect local machines is to put a hardware firewall between the local net and the cable/DSL modem. These can be had for $75 – $100 and protect the entire net. Or roll your own with a specialized Linux firewall distro and put everything else behind it. Otherwise, there will be holes between the different local systems, and if one falls, then any trust relationships between the systems will cause the entire local net to fall. If you are really paranoid, use both hardware and per-system firewalls. Per-system local firewalls on a local net without a hardware firewall is bad architecture.
Use the force, Jed. You aren’t on Windows any more.