We’re fairly oblivious to the amount of data our smartphones hold about us. It’s something we well and truly take for granted. Today we store almost everything in our smartphones – from our bank details to our emails and even our day-to-day calendar. So if our smartphone, or the data it holds, gets into the wrong hands, it can have disastrous consequences.
There are ways around this, however, with plenty of things you can do and download to your device to reduce the risk of having important information swiped from your phone.

Below you’ll find some of the more secure methods, all worth considering in an age where we rely so heavily on our mobile devices.
1. Install a VPN
A VPN, or Virtual Private Network, is useful for a lot of things, like improving security.Most of us have few problems connecting to public Wi-Fi hotspots, but in reality, we don’t know how secure they are and also who else is connected to it. A VPN allows you to camouflage yourself from the network and browse anonymously, offering that extra layer of security.
There are dozens of great VPNs out there, with CyberGhost often touted as one of the standout names. You can check out this CyberGhost review for more details on how it boosts the security profile of your smartphone, and also of your desktop.
2. Download an Antivirus
One of the more obvious, and indeed safest, options is to download an antivirus software to your device. Very few of us download antivirus as an app, but it’s wrong to assume our mobile devices won’t be infected.
You’ll often be able to use the same package as what you would on your desktop computer so it may cost you nothing to do. Even so, a mobile only antivirus won’t cost huge amounts and it can save you tremendously.
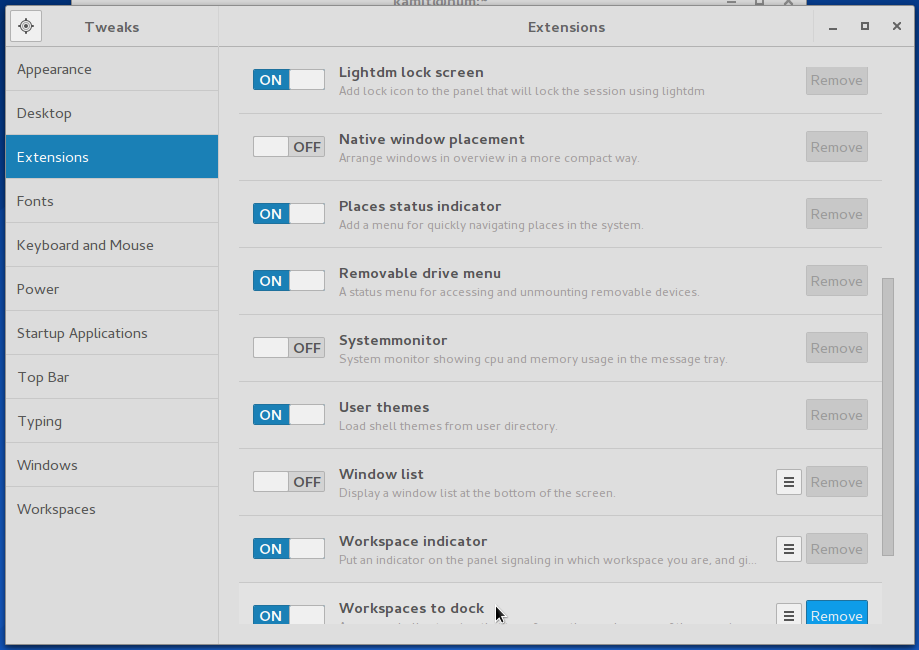
3. Manage Your Software Permissions
Something that won’t cost you a penny is simply managing the permissions within your apps. There are relatively simple ways to do this on both iOS and Android devices. Proper configuration of software permissions should give only trusted apps access to your mobile data and other apps such as Facebook or your Google Play or App Store account.
4. Use A Password Manager
It goes without saying that using the same password across multiple accounts isn’t the safest way to manage your affairs. If a hacker gets hold of one password, there goes, as they say, the whole neighborhood. Using strong alphanumeric passwords is the recommended thing to do, but remembering them all can be tough.
A password manager is perfect for getting around this and can not only remember all your passwords but generate incredibly secure ones that are almost entirely hacker proof. There are tons of great apps to do this, all costing a small amount. It’ll save you time and boost security on your mobile tenfold.
5. Set Up Remote Tracking & Wiping
It can feel like the end of the world when you lose your smartphone. All that data now in someone else’s hands. Fortunately, tracking and wiping allows you to wipe all your data and minimize the damage. And you don’t need an app installed to do so, although there are plenty out there to make this process easier. You can use Android Device Manager to do this, although it is very much a last resort as ultimately your device could already be in the wrong hands.