Fedora 23 Security Lab is Spin of Fedora, a Linux distribution sponsored by Red Hat.
Fedora spins are editions of the popular Linux distribution that use desktop environments other than that used on the main Fedora edition. That main (Fedora) edition uses the GNOME 3 desktop in its default form.
As the name suggests, the Fedora Security Lab Spin is expressly for designed for security purposes.
The following is from the project’s home page:
The Fedora Security Lab provides a safe test environment to work on security auditing, forensics, system rescue and teaching security testing methodologies in universities and other organizations.
The spin is maintained by a community of security testers and developers. It comes with the clean and fast Xfce Desktop Environment and a customized menu that provides all the instruments needed to follow a proper test path for security testing or to rescue a broken system. The Live image has been crafted to make it possible to install software while running, and if you are running it from a USB stick created with LiveUSB Creator using the overlay feature, you can install and update software and save your test results permanently.
That puts it in the same category as Kali Linux, CAINE and similar distributions that I’ve compiled in Pentesting, digital forensics, and hacking distributions.
I have already published screenshots from test installations of the Fedora 23 KDE Spin and the Fedora 23 Cinnamon Spin. In this post, you’ll find screenshots from a test installation of the Fedora 23 Security Lab.
It ships with the latest Xfce desktop environment, the same version used on the Xfce Spin. This screenshot shows the default desktop.
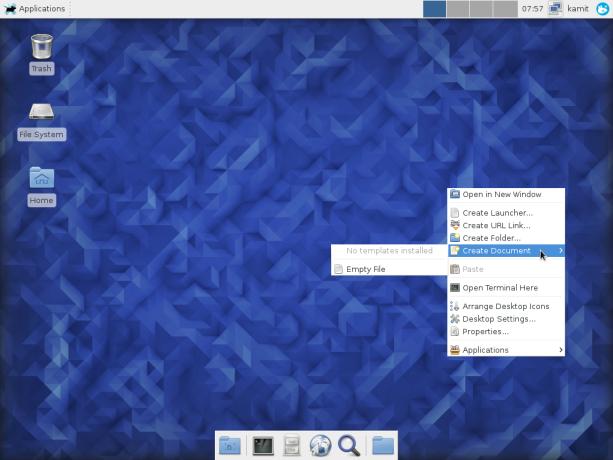
Figure 1: Default desktop of Fedora 23 Security Lab
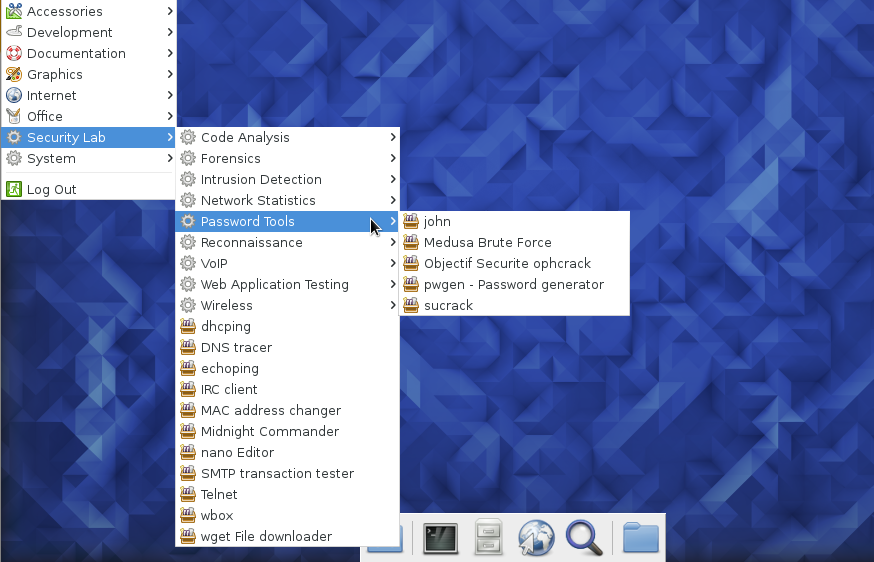
Like Kali Linux, CAINE and others like them, Fedora 23 Security Lab comes with standard applications that you’ll find on other distributions designed for daily desktop computing, besides those targeted at more experienced users and security professionals. On Fedora 23 Security Lab, you’ll find those applications under the Security Lab menu category, as shown in this Figure 2.
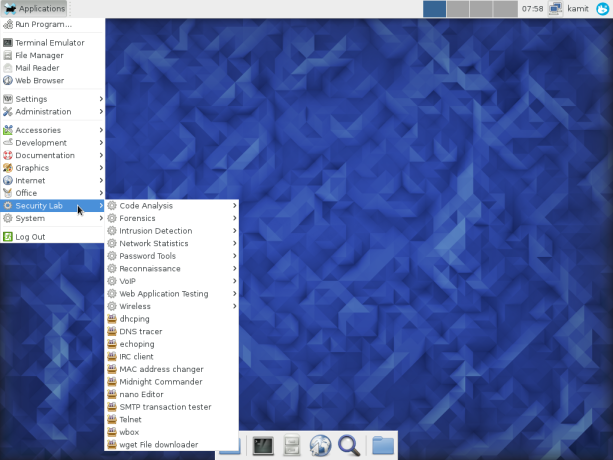
Figure 2: Desktop menu of Fedora 23 Security Lab showing the Security Lab applications menu category
The rest of the screenshots shows the entry in each sub-category of the main Security Lab category.
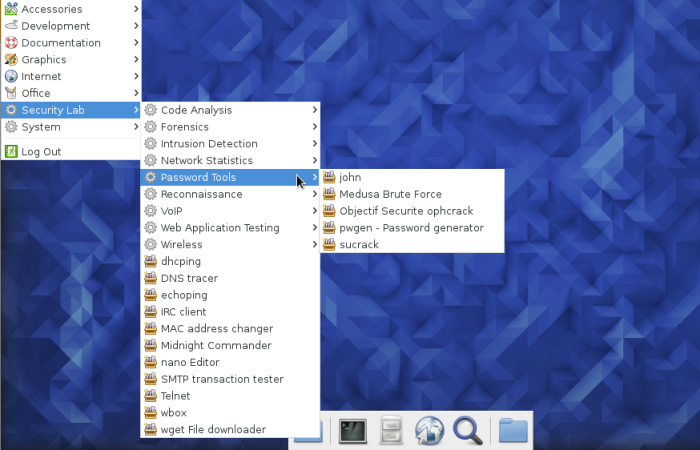
Figure 3: Password-cracking applications on Fedora 23 Security Lab

Figure 4: Wireless hacking applications on Fedora 23 Security Lab
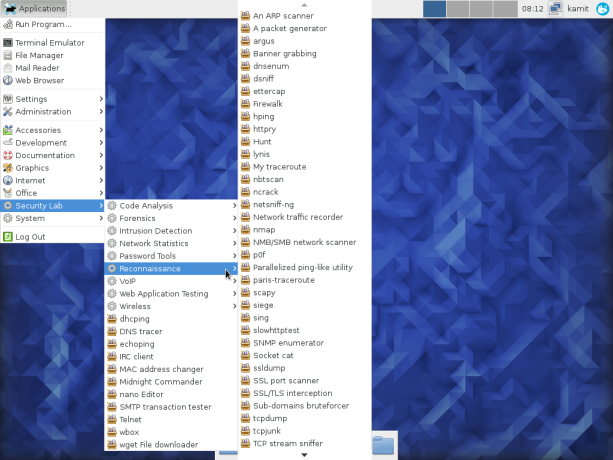
Figure 5: Reconnaissance applications on Fedora 23 Security Lab
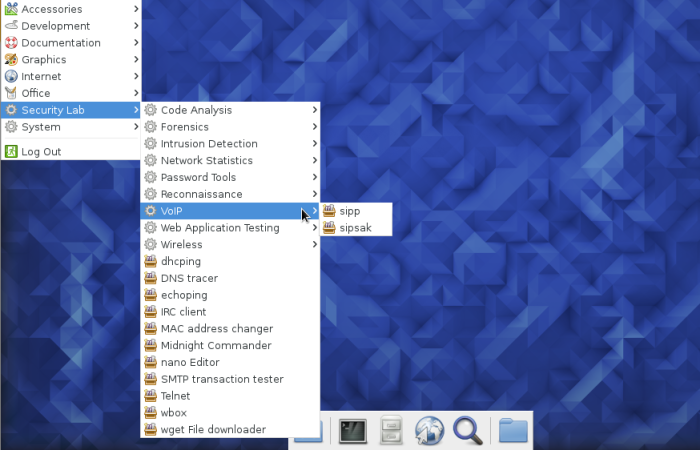
Figure 6: VoIP hacking applications on Fedora 23 Security Lab

Figure 7: Web application testing tools on Fedora 23 Security Lab
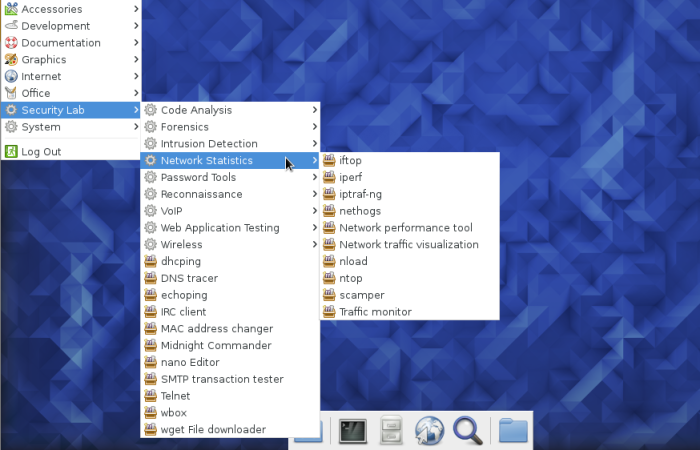
Figure 8: Network statistics applications on Fedora 23 Security Lab
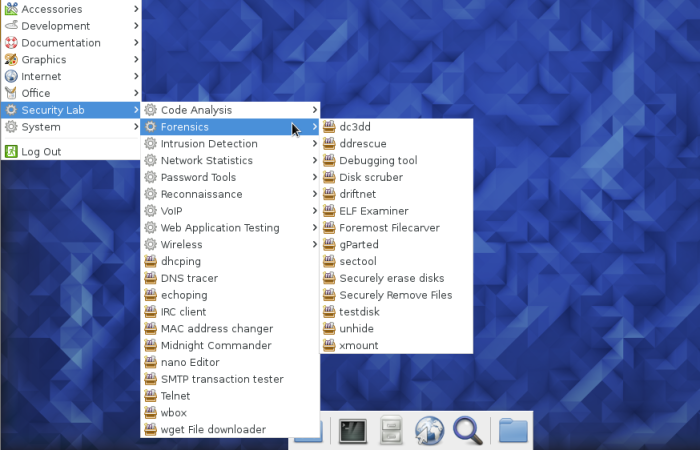
Figure 9: Forensic applications on Fedora 23 Security Lab
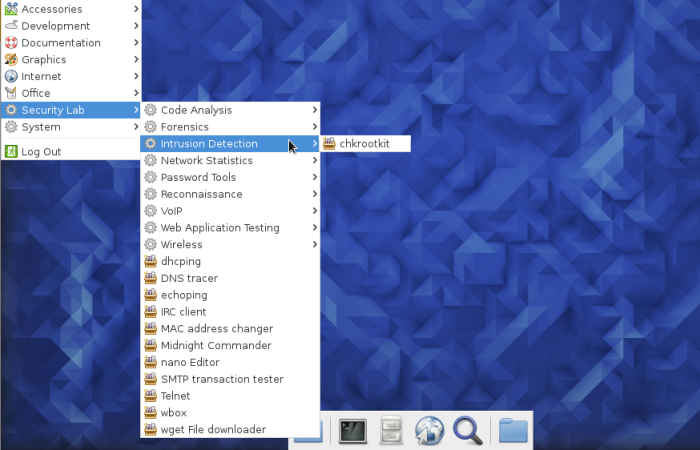
Figure 10: Intrusion detection applications on Fedora 23 Security Lab
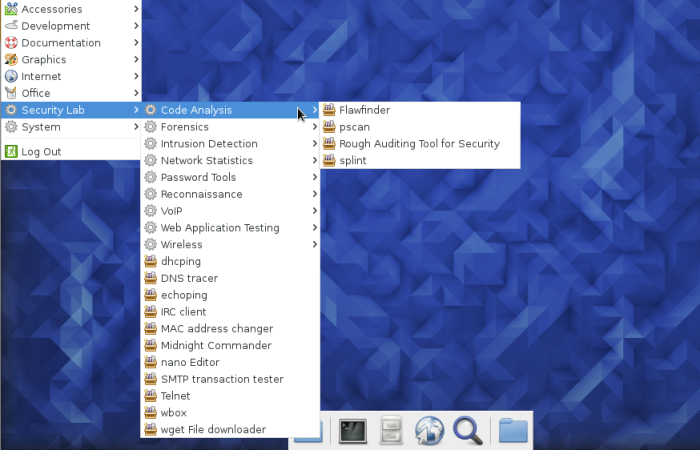
Figure 11: Code analysis applications on Fedora 23 Security Lab
Compared to Kali Linux, CAINE, BackBox and others in Pentesting, digital forensics, and hacking distributions, Fedora 23 Security Lab is more of a general purpose security distribution, and is thin in the number of applications installed under some of the sub-categories, like the VoIP sub-category, which has just one application installed. That means you’ll have to dig in the repository for more of such applications. If you don’t mind doing that, installation images of Fedora 23 Security Labs are available here.
If you need a security distribution that’s more specific, try any of those here.