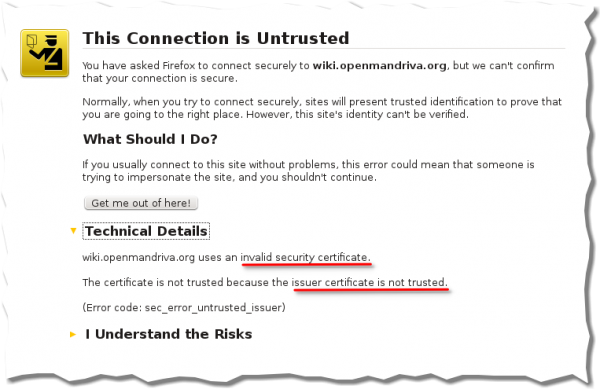
Nothing drives away visitors to a website faster than seeing a warning message that informs them that the site or page they clicked to visit is not trusted.
It’s a guaranteed traffic killer. No Web publisher wants visitors to see that type of message. But that is exactly what they will see if the publisher uses an SSL certificate issued by CAcert.
Why? Because nobody that matters in the industry seems to trust CAcert as a Certificate Authority. If you are wondering who or what CAcert is, it is a “community driven Certificate Authority that issues certificates to the public at large for free.” And their goal is to “promote awareness and education on computer security through the use of encryption, specifically with the X.509 family of standards.”
The problem, as stated earlier, is that browser vendors do not ship CAcert’s root certificates by default. Why? It’s a long story, but the gist is, they don’t trust the certificates. So if you are a Web publisher and are considering a CAcert-issued digital certificate, do yourself a favor and get one issued by a trusted certificate authority. Yes, they cost money, but the traffic (and money) you lose from scared visitors could be more than you spend for a commercial certificate.
I decided to write this article after I saw the usual “invalid certificate warning” when attempting to visit OpenMandriva’s wiki page. Yes, you may opt to add an exception to the certificate, but most users, including this author, will simple click the back button or close the browser tab or window.

With its bright-red background, the warning looks even more ominous if you tried to visit the page using the Chromium browser. So whoever is in charge of OpenMandriva, here’s a friendly message: Please get a digital certificate from a trusted source.






Oydenos recommends Perspectives.