Privilege escalation: Offline password cracking applications.

Privilege escalation: Online password cracking applications.

Privilege escalation: Sniffing applications.

Privilege escalation: Spoofing applications.

Maintaining Access: Tunneling applications.

Maintaining Access: Web backdoor applications.

Reverse Engineering Applications.

Social Engineering: Honeypots applications.

Forensic Analysis: Acquisition applications.

Forensic Analysis: Data recovery applications.

Forensic Analysis: File analysis applications.

Wireless Analysis: Wireless cracking (aircracking-ng) applications.

Wireless Analysis: Wireless scanning applications.

Miscellaneous: Stress-testing applications.

Miscellaneous: Wiping applications.

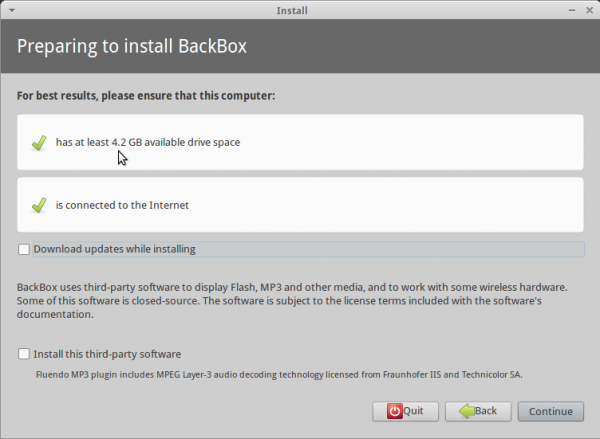
Resources: You may download a 32- or 64-bit installation of BackBox 3 from here.



made a reviw of Linux Backbox here http://divtech.pp.ua/?p=287