Wuala is a cloud storage service by LaCie, a computer storage and display outfit. Like all cloud storage services, Wuala makes it easy for you to backup, sync, share and retrieve your data from any location. How does it differentiate itself from the rest of the pack?
Well, LaCie claims that Wuala is different because “All files get encrypted and are stored redundantly. No one unauthorized – not even Wuala as the provider – can access the files.” Essentially, your data is encrypted locally, on your computer, before it gets uploaded to a server in some remote location.
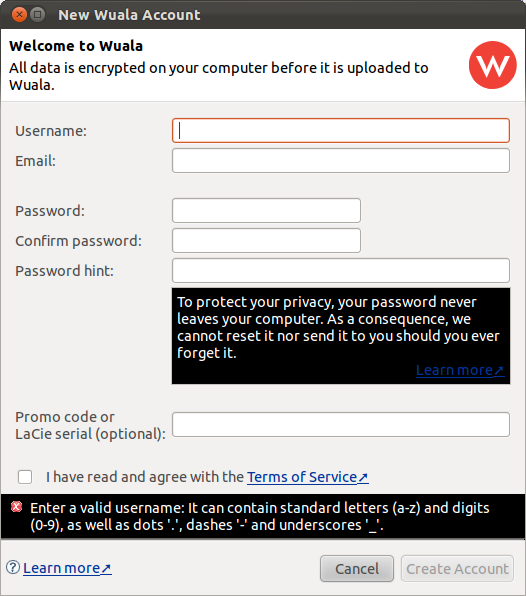
But how does the system work? It starts with you installing the Wuala client on your computer, followed by an account creation process. Your account password is used to encrypt your data, with the password not transmitted over the wire. Since your password never leaves your computer, nobody else but you know what your password is. So nobody should be able to decrypt your data. The screen shot below shows the account setup screen.

Sounds good, but could there be a backdoor? And why am I even raising that possibility? It stems from a fundamental understanding of how these things work. You see, the password you specify is used to encrypt and decrypt your data, but it is not the encryption algorithm, which we do not know anything about.
That, plus aspects of the Terms of Service, which I took the time to read, makes me think that under the right circumstances, you might not necessarily be the only person that can read your data.
This paragraph in the terms of service, under Use of Service, makes me feel very good about it:
LaCie agrees that all files you store using the Service, including their metadata (file name, description, comments, thumbnail images, etc.), (“Data”) will be encrypted such that they can neither be read by LaCie nor by any third party, unless the Data is explicitly shared or made public by you. LaCie has no access to your password, does not know it and cannot reset or recover it. You acknowledge that if you forget your password, your Data will be irrevocably lost.
But not this line, under the same section: “As part of the evolution of the Service, LaCie may discontinue, modify or add new features to the Service without prior notice to you.”
The paragraph that made me very suspicious about how private the service is, is this one, under the Privacy section:
“Customer agrees that LaCie may transmit any data stored by Customer to a third party if LaCie believes in good faith that it is required to do so in order to: (a) comply with any law or order issued by any legal authority; (b) avoid infringement of the rights of a third party; or (c) protect the property of LaCie or the personal safety of its users and the public.”
In other words, if LaCie gets a simple letter from a government entity that says, “Give us the data from customer Joe Blow,” they will comply, which they must, under current laws. That leaves the possibility that there could be a chink in the encryption armor (read backdoor) that could make it possible for somebody other than you, to read your data, even without your password. Use these services with care. If I had data that I wanted to keep private, the only way I would use Wuala or any other cloud storage service will be to encrypt it first, before uploading it.







With Wuala i lose 700 GB
http://www.swisscastles.ch/wuala
Baaaaaaaaaah, Wuala got a gift of their life from Snowden. Anyone hosting whatever within US/UK/NZ/AU is just crazy.
@Gianluca: Did you already notice users migrations? Are you getting more orders?
Canada?
Nopes, Cyprus
We have been using the program for about 2 years and have many many problems on every computer ranging from 2 to 3 bluescreen crashes per day on a Windows 7 PC, which only happens when working on an Office 2008 file and writing an email at the same time. Other issues include Read Only files that have to be resaved, loss data due to crashes, folders that can’t be deleted as they just keep coming back, files that disappear out of folders or show 0KB, etc, etc. We also have MACS that have the same problems except for the blue screen crashes. Support is also virtually non-existant. As for privacy, it seems to be secure but that’s about it. Over all I would not recommend Waula for any business or personal use unless you can afford data loss and have a lot of time on your hands to deal with software problems on a daily basis.
We have since switched to Drop Box and have had virtually no problems except for when we were copying the files from Wuala and I’m pretty sure missing files were again caused by Wuala. Good riddance!
@Gianluca no open source client = no trust
Whatever you will say is useless. Wuala can push at any time an update to “steal” the user’s password if a judge asks for it.
A judge has power to covertly force a software company to sit down and develop code, “push” the update (on a Linux system?) and target one specific user to steal their password and forward it to the judge? Um… no. This is as safe as Spideroak. Spideroak will have to comply with any orders requiring them to turn over data as well… the point is that the data is encrypted and the password never touched their servers, so there’s no way to turn over what they don’t have. As a boss of mine used to say about paper trails, “One cannot audit what there is not.” 🙂
But the client could easily be updated (and the terms of service, too) to capture passwords, without informing anybody.
So could the Linux kernel if Linus Torvalds gets hit on the head and turns into Evil Linus. I don’t lie awake at night worrying about that.
Hi!
The only provider I really trust in terms of security is Spideroak. They have pretty much centered their whole business model around that issue. If you like you can listen to my interview with Spideroak CEO Ethan Oberman:
http://www.cloudbackuping.com/interview-with-spideroak-ceo-ethan-oberman/
Now, in the post-prism era, we just wait to see how quick SpiderOak will be forced to shutdown, like LAvabit or to cooperate 🙁 🙁 🙁
Hey there, this is Gianluca from the Wuala Team. Thanks for your interest in Wuala. Rest assured that there is no backdoor (unless the NSA managed to put one into AES or other cryptographic building blocks, but in that case, your tipp of separate encryption does not help much either). For 99.9% of the users, the thing to worry is malware with keyloggers and weak passwords.
Best,
Gianluca (http://wuala.com/en/about/)
OK, nice that the wuala team is monitoring this discussion.
I would prefer the old rule of the cryptography “popes” who say what makes a safe cryptographic system:
1)A safe algorithm
2)code an priciple must be open
3)you can have plain/encrypted samples
4)you don’t have the password
= no attack on your privacy is possible.
In that sense I would prefer if WUALA would open its code for review by renowned specialists.
So far I’m not convinced completey of the trustworthyness of the WUALA solution.
Remember what happened to PGP, when the PGP code was not disclosed anymore by “Network Associates”?
Brgds, Mike.
Just keep this in mind; do not trust any cloud service to protect your privacy. They are required by law to hand over info on any account on their service, if any govt agent/agency requests for it.
Also. a govt sometimes succeeds in having them build a backdoor into their application.
That applies for the majority of Cloud Storage providers. However, not for Wuala.
More details by blog posts from Wuala’s CTO:
http://wuala.com/blog/2012/02/court-rules-you-cannot-be-compelled-to.html
and
http://wuala.com/blog/2011/12/patriot-act-and-cloud-storage.html
Best,
Gianluca