In a world of always-on connectivity, Internet of Everything and Internet of Things, where most devices now have an embedded computer, the risk posed by hackers tampering with them cannot be overlooked.
I don’t have a smart meter at home, but in the near-future, most homes, including mine, will have one. That’s why I like to read and learn as much as I can about the security risks they pose.
And that’s why I’m linking to an article titled Smart Meter Attack Scenarios, written by Rainer Link, a Senior Threat Researcher at Trend Micro, a security outfit with global operations.
Here’s an excerpt
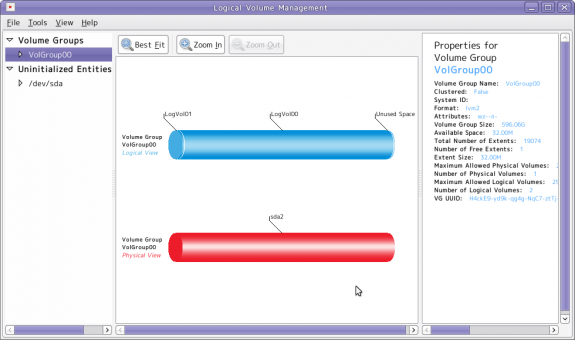
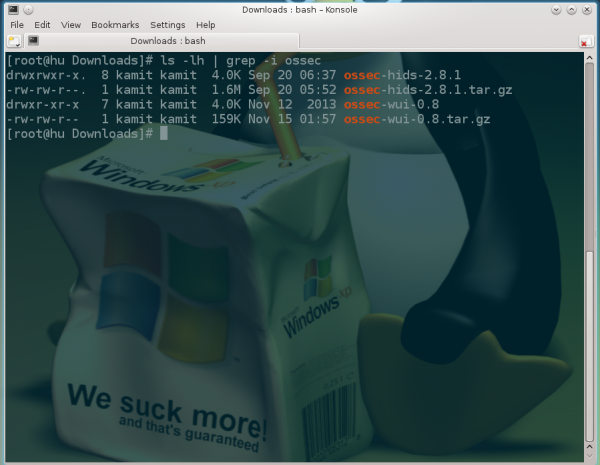
At their heart, a smart meter is simply… a computer. Let’s look at our existing computers – whether they are PCs, smartphones, tablets, or embedded devices. Similarly, these smart meters are communicating via understood technologies: cellular connectivity, power-line networking, or the user’s own Internet connection.
With that in mind, we have to consider the possible threats – what could happen if a smart meter is compromised? Similarly, what are the problems that could result if the connectivity of a smart meter is disrupted? Let us see.
Perhaps the most obvious risk is simple: meter tampering. If a smart meter can be hacked, inaccurate information can be sent back to the utility, allowing an attacker to adjust the reading and resulting in an inflated bill. Let’s say, for example, that you have an argument with your neighbor. In revenge, if he can access your smart meter, you might see a rather large electric bill.
You may read the complete article here.

The above screenshot was taking from The Risk of Adopting a Smarter Energy Future video.



























Smart meters are a real boon for burglars.
If the usage information can be retrieved from the smart meter or the utility company’s web site by cracking into the customer’s web account, it is very easy to see a pattern when there is minimal power consumption and therefore the time period when the property is most likely vacant.
And if the burglar alarm is internet connected as well, well it might be possible to crack that because of careless password protection.
Not just for burglars, but any hacker looking to have some fun.
So I guess in the very near future, hacking a smart meter, like hacking drones, will be for fun and profit.