Why is it even necessary to convince anybody that they need a firewall enabled on their Internet-facing computer – desktop or server? You would think that the role of a firewall should be obvious to any computer user. However, some of the comments that I have come across on this subject tell me that is not necessarily true.
Take for example this comment on the Chakra forum:
I’m also against firewall (how many people surf with a usb modem on linux, or disable router firewall??), but MAC to me is lame. What kind of porn site or what kind of script you should visit/run to get malware on linux? and since perhaps three guys in a thousand usually download and run script without reading it, should I have my computer bloated with these pieces of software? Seriously: how many time you ran amarok, or vlc and find an exploit blowing up your pc?
Or these from PCLinuxOS fanboys:
Just about all distros include a firewall but it is disabled by default. I don’t believe in the “one firewall configuration fits all” theory. My needs are different from yours. Include a firewall, place an icon somewhere easy to spot and let us do the rest.
…The firewall was originally turned on, but the majority of users complained about it so the developers turned it off. Personally this should be left to each and every user to decide if they want it or not.
…They prefer the Firewall icon on the desktop so they can configure it themselves based on their own personal needs.
What those comments reveal is that many in our community do not understand the basics of network security. I hope this short article will shed some light on the topic.
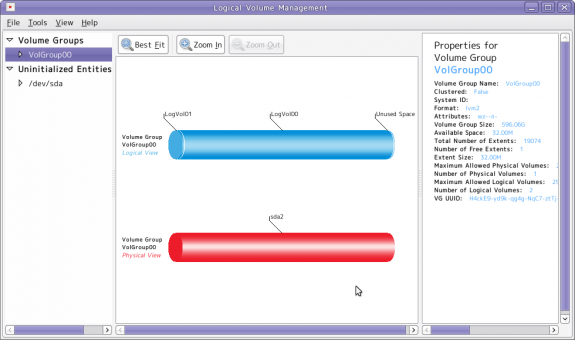
Central to this discussion is a fundamental understanding of the role a firewall plays in the overall security posture of a computer or computer system. In simple terms, a firewall protects a computer from network attacks. And there are host-based and network firewalls. A host-based firewall is the one running on and protecting a single device. That would be the one running on your personal computer, whether it be running a Linux, BSD or any other operating system.
On the other hand, a network firewall is the one running on a device on the edge or perimeter of a network. That device could be a router, switch or VPN device. Your cable, DSL or Fiber Optics router falls in this category. The mistake that most people make is in thinking that if they have a firewall on the edge device, then none is needed on the personal computer sitting behind it. Very bad thinking.
In a computer network, one open to access from the outside, best security practice calls for each node in the network to have a security posture of its own, one that works in concert with the perimeter firewall (and also with other security measures). The professional jargon for this practice is Security in-Depth. It is a layered approach to securing a network and this approach is not unique to the computing world. You can observe it anywhere you look. For example, assume that you live in a walled compound, do you leave your doors and windows unlocked simply because you have a fence around your home? Of course not. Or do you leave your car unlocked just because it is parked inside? Most likely not. The reasons are obvious.
The same thinking and principle should apply to your local network. Aside from a perimeter firewall, the one running on the device on the edge of your network, there should also be a host-based firewall, one running on your desktop, server, notebook or netbook computer. This layered approach ensures that if there is a breach in your perimeter defense, if somebody jumps the fence, that your computers are not left wide open to the intruder(s).
So, just because your computer is sitting behind a cable, DSL or fiber optics router with a firewall enabled does not negate the need for a host-based firewall. Security in-depth.
The best firewalls are capable of Stateful Inspection (or Stateful Packet Filtering), which dictates that all outbound connections are allowed, while all inbound connections that are not related to an outbound connection are blocked. That is, an inbound connecting that does not have a related entry in the state table is not allowed.
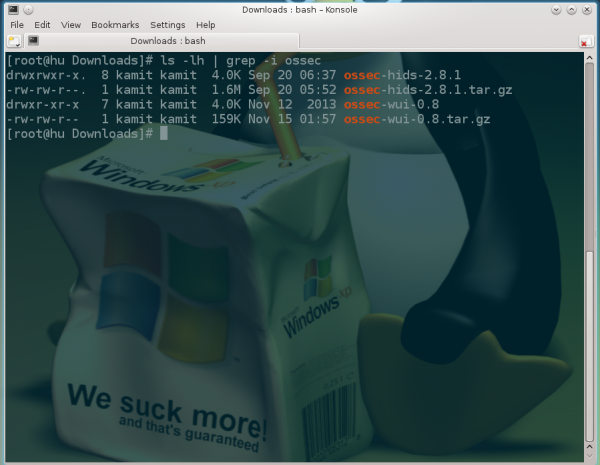
Some of the better Linux distributions, like Fedora, have a firewall enabled out of the box. That is the way it should be. And that is why I always comment on the security posture of any distribution reviewed on this website. It is that important. The Linux kernel has a firewall built-in (true also for the BSDs), and there are several graphical management interfaces for managing it. The least we expect from distro developers is to have it enabled out of the box.


























Wow, I have to say I was really disappointed in this post. I am a believer in not having to over run my entire home network with firewalls that I feel will cause more hassle then resolve issues for me. I read this post in anticipation that you might change my mind, only to reach the end and find that you have not provided a single reasoning, example or excuse for me to turn on firewalls for one of my PC’s let alone every single device I have attached to my network.
On top of this, if you are unfortunate, or silly enough to already get malware (virus, worm,etc) on your machine, the chances are you’ve ran in a escalated privileges and it’s already manipulated any possible firewall settings you have on your local computer, rending your local firewall useless.
The same principle is there on ALL operating systems.
I happily leave my windows and doors open because it allows me to breath fresh air and I’m secure in my area because I monitor it.
I’m not saying that having a local firewall isn’t protecting you more, I am saying that in the long on going battle between usability, friendly and functional environment, Versus tight security has to be taken into consideration. It is only better to prevent rather than cure, if the cost and effort deems so.
Can you elaborate more on what is your opinion the difference between the need for firewalls on Linux and Windows?
If there is a difference, somebody will have to explain it to me. I’m more interested in a principle than in the OS a PC is running.
Nice post. I’ve translated it to Spanish and I’ve posted it on my blog. I hope you do not mind. If do, Tell me and I remove the post.
Regards.
That’s cool.
Topics like this I like! I don’t get why some people are making a deal about “scaremongering”.
If a user can stop all services that normally listen for connections and still have a usable machine, then of course a firewall is not necessary. This is perhaps easier on Linux than Windows with its myriad of cryptic services running. A Linux machine can have by default a number of open ports: CUPS, SSH, RPC-bind, etc. So a firewall can certainly benefit.
As others have commented however, I too question the necessity of a local firewall when inside a “secure” network, especially when using Linux. Also, all home networks sit inside of a router that has to be explicitly configured to forward incoming traffic to some inside host, therefore no generic inbound connection can be routed to some specific machine. So, no need to run a firewall in your home network.
It’s a different story of course when roaming with a laptop / netbook on WiFi, connecting to whatever network is available. You definitely need to run a firewall in this case.
You’re absolutely right…a NAT’ed connection behind a standard router or modem is enough. Go ahead and try to ftp to my local machine I’m commenting with now…it won’t work because the port isn’t forwarded to it.
I have NEVER run a local firewall on any of my systems and I’ve used Linux since 1995…when I roam with my laptop, guarddog or something similar works.
What happens if the bad guys succeed in breaking in your router and attack you from there? What happens if, say through a security hole in the machine used by your wife someone attacks yours?
That’s the point few seem to understand, and that’s the underlying principle behind Defense in-Depth.
your premise is incorrect.
defense in depth is not a best practice, it is a compromise practice to deal with threats originating inside your network.
ever heard of a trusted network? Study more.
The premise is not something I dreamed up, it’s an industry standard. Perhaps you should read this for a better understanding of what we are talking about. Search the Internet for Defense in-Depth or Security in-Depth, and then try and convince yourself that “defense in depth is not a best practice.”
I agree, a host-based firewall brings an additional layer of security, but it gives you a wrong feeling of security. And it is not necessary if you don’t expose any services to the outside world. Moreover, a lot of threads still come via email, as PDFs, JPGs whatever and from browser exploits and insecure plugins (think flash). Your firewall will not protect you from those.
A packet filtering firewall is supposed to work in concert with other security features. That’s why we have security tools like application-level “firewalls.”
And that is why in Ubuntu, for example, AppArmor is enabled out of the box. In Fedora, SELinux is enabled out of the box too. AppArmor, SELinux and similar programs are application “firewalls.”
Hey, I installed Firestarter in Debian Squeeze, and have run the wizard but have not applied any rules, is the firewall active?
I know its started whenever my PC connects to the network or during “dailout” thats what it says.. does it block the unwanted ports by default? or do I need to change the config/rules to make it work?….could you shed some light upon this?
Thank you for the insightful articles and clear How tos!
For somebody who is not very familiar with firewalls, Firestarter is not a good option. Try any one from this list.
By default, the firewall should be in Stateful Inspection, that is, allowing all outgoing connections, while blocking or denying all incoming connections that do not have a related entry in the state table.
After that, if you want to allow a service to be accessed from any other computer (from your LAN or the Internet), you have to create a rule for it. With the graphical tools, that is pretty easy.
Si in your company every workstation is running a firewall in addition to the corporate network security?
How many network security layers do you think any enterprise has in place?
Depends on the company… note enough or way toi many …
“You would think that the role of a firewall should be obvious to any computer user.”
Are you kidding? In my experience, most users don’t even know what a firewall is.
Isn’t that part of the problem?
“The mistake that most people make is in thinking that if they have a firewall on the edge device, then none is needed on the personal computer sitting behind it. Very bad thinking.”
I guess I’m a “very bad thinker”. If someone can penetrate a correctly configured firewall on the router, then I see no reason that a correctly configured firewall on the pcs would stop them.
Like the previous poster, I only have ssh open on my external router, with passwords disabled. Good luck getting inside.
well, boo-hoo! and good luck with this kind of scaremongering. i have stateful firewall on my gateway (pfsense), but no firewalls on my linux machines, only on the windows pcs (where is definitely needed). please, please, please, break into my network, if you can, and infect my linux machines (can’t vouch for the windows one)! i dare you!
You find an article about an established security practice “scaremongering”?
Security in-Depth or Defense in-Depth is “scaremongering”? Nice try.
@jackd:
It’s about following security best practices. Understand the principle, and you will not be posting the type of comment you just posted.
We all should be driving tanks then eh? Afterall, they’re the most defensible vehicles and we have to be careful with all those other scary vehicles out there right? I mean, best security practices and all.
Don’t mean to throw a wrench into your thinking but firewalls have their place and on a Linux desktop behind a router/modem using NAT a firewall is overkill. Instead of blocking ports…just don’t open them in the first place. For example, don’t install an ftp server on your desktop. Don’t install MySQL server on your desktop. Don’t install Apache on your desktop.
So, if my PC will not have any services running, and not ports accepting connections. Why should I need a firewall? If there is a remote exploit in the network stack, then the kernel firewall will most probably not portect me. And if I will block all incommings, why open the listening ports anywhays?
K.
I’ve had my linux computers open to the Internet for years and years. Not so much as a bit of a breach. How do I do it? I set my router up so that only ssh is allowed in, and I set up ssh on my computers so that only passphrases are allowed for remote access. Sure, I could get DDOS’d, but who would bother? Nothing important going on. Breached? Go ahead, make my day! And…
Good luck with that.
So Debian is wrong ?