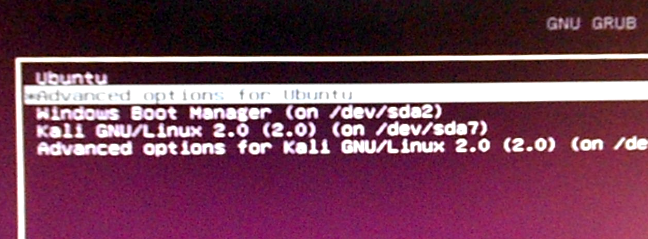
Password-protecting the bootloader is one method you may employ to enhance the physical security profile of your computer. GRUB, the GRand Unified Bootloader, is the default bootloader on virtually all Linux distributions, but on a significant number, the installer does not have support for setting a GRUB password. This article presents the step involved in password-enabling GRUB – on a running system.
Before we go through the steps involved in setting a password for GRUB, it’s best to understand why this is even necessary. Principally, we password-enable GRUB to:
- Prevent Access To Single User Mode — If an attacker can boot into single user mode, he becomes the root user.
- Prevent Access To the GRUB Console — If the machine uses GRUB as its boot loader, an attacker can use the edit the command’s interface to change its configuration or to gather information using the cat command.
If your distribution’s installer has support for setting a GRUB password, the process involved should be similar to the one shown in the image below, which was taken from a similar Fedora 13 tutorial. Just check “Use a boot loader password” and the installer will prompt for a password.
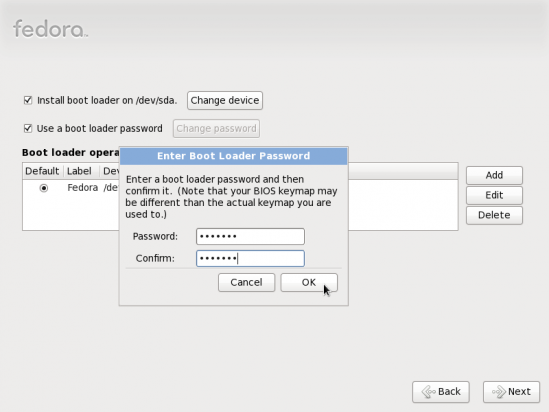
Specifying boot loader password
If your distribution’s installer does not have support for setting a password for GRUB, you can still do it after installation. The process involved in this exercise is the same across distributions. However, for this article, an installation of Fedora 13 was used. Here are the steps involved:
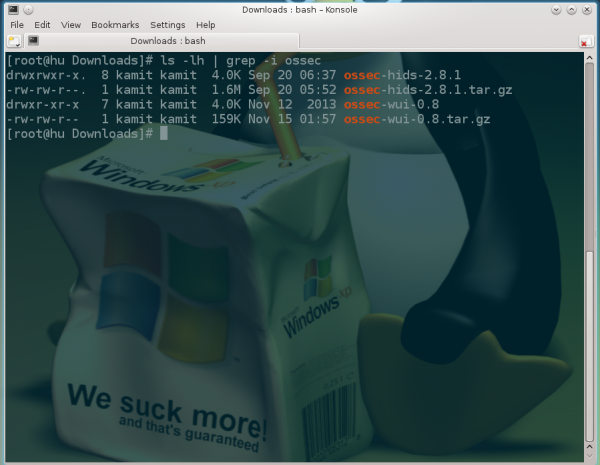
- From a shell terminal, run the grub-md5-crypt command. The password that’s requested will be the one that’ll be used to protect GRUB. It should not be the same as that of any user account on the system, certainly not the same as the root password. Note the md5 hash generated. You will need it in the next step.
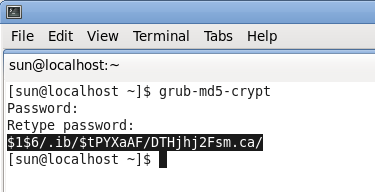
Generate the md5 hash for password-protecting GRUB
- Edit /etc/grub.conf as shown in the image. Just add another line below the “timeout” line and type in password –md5 (md5 hash generated from step 1) as shown in the image. Save the file. Reboot and try to access other features of GRUB by pressing the “p” key. Did it work?
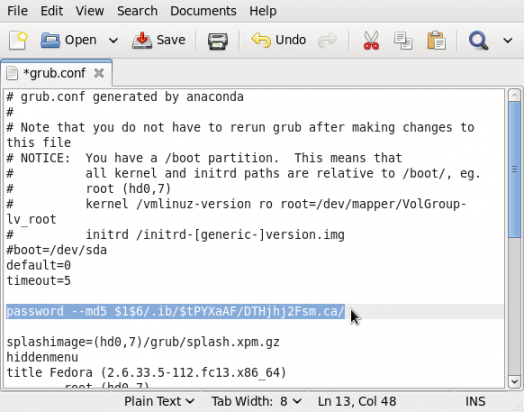
Edit grub.conf
Complete this simple process, and you would have taken a small but significant towards enhancing the physical security profile of your computer.


























I thought you had to add the ‘lock’ option to each entry in the grub?
Does this password-protect the computer from booting at all? Can we prevent individual GRUB entries from being booted without the PW, but let others boot without a PW? The practical and real-world uses are a bit light on details here…
It does not. The reasons for password-enabling the GRUB (or any other bootloader’s) console are given at the top of the article. To prevent the computer from being booted by unauthorized persons, you will have to configure full disk encryption. Full disk encryption and password-enabling the GRUB console are just one of several methods you may use to enhance the physical security profile of your computer.
“Can we prevent individual GRUB entries from being booted without the PW …?” In a dual-boot configuration, yes you can.